Protect Your Online Identity: A Comprehensive Guide to Hiding Your Identity Online
When engaging in online information retrieval, your personal data becomes susceptible to risks. Advertisers actively accumulate valuable data derived from your browsing history. To illustrate, if you input search terms like "gym" or "weight loss" into the search field, an advertiser might deduce your interest in fitness or weight management and subsequently send you pertinent advertisements for related products and services.
Although these practices fall within legal boundaries, malevolent actors can also exploit your data for personal gain. For instance, cybercriminals can vend your credit card details on the clandestine portions of the internet. It is apparent that hackers and illicit individuals can illicitly access online marketplaces or banking systems to procure your private information, resulting in grave consequences. They can utilize any content you share online, underscoring the utmost importance of safeguarding your personal data.
How to hide your identity online?
Employ incognito mode

The issue of online privacy has garnered significant apprehension among numerous individuals, as nobody desires their personal information to fall into the wrong hands. Several measures exist to safeguard personal data, and one such measure involves employing the "incognito" mode while browsing the web. Initially introduced by Apple in 2005 within the Safari browser, this feature was subsequently adopted by other prominent browsers such as Google Chrome, Internet Explorer (now Edge), Mozilla Firefox, and Opera between 2008 and 2010.
Utilizing incognito mode allows users to conceal information and solely disclose user data to acquaintances and family members (local users). However, despite this mode, internet service providers (ISPs), Wi-Fi owners, website administrators, and local network overseers can still access user browsing records. While incognito mode may assist users in concealing their identities from immediate scrutiny, we maintain skepticism regarding its true anonymity. Both Firefox and Google Chrome have issued warnings, reminding users that even in incognito mode, service providers can still perceive all user browsing records and associate them with the computer's proprietor.
In a workplace setting, users' internet activities can be traced by local system administrators. Companies often employ targeted tracking of employees' visits to specific websites (e.g., social networking platforms, instant messaging services) to prevent time wastage. It is important to note that incognito mode proves ineffective in such scenarios. Specialized software enables administrators to swiftly monitor employee visits, capturing details such as the visited site, timestamp, duration, and utilized resources. Therefore, ensuring the safety of personal data remains paramount, necessitating efforts beyond solely relying on incognito mode to fortify online privacy.

Contemplating methods for hiding your online identity? Enter Tor, a technology that effectively conceals one's identity and fosters heightened internet safety. The fundamental concept behind this network revolves around bestowing anonymity and security within an environment where mutual distrust is prevalent among most participants. The crux of the Tor network lies in encrypting and relaying data through multiple computers, thereby altering their IP addresses and establishing a secure conduit for data transmission.
- How does it work to hide your identity online?
Tor operates akin to a scene from a cyber-thriller film: it connects a user to a desired site or service by traversing several servers, typically involving three nodes—namely, a guard, an intermediate, and an exit relay. Prior to the request or data entering the network, a specialized program on the user's computer encrypts it in a manner that each server can solely decrypt a portion of the data.
To enhance web browsing safety, individuals commonly resort to utilizing the Tor browser, the official browser developed by the network's creator, which encompasses all the necessary configurations for connecting to the Tor network. Initially, connecting to the Tor network necessitated a certain degree of technical prowess, but over time, the process has been streamlined. Presently, anyone can download the Tor browser onto their computer and initiate it to embark on a safer surfing experience.
- Is it a perfect choice?
Nevertheless, the Tor Browser harbors its own set of noteworthy limitations, warranting careful consideration before utilization:
Firstly, it is crucial to acknowledge that not all data remains impervious to vulnerabilities. When employing plugins and add-ons, it is imperative to bear in mind that they transmit your data to their respective developers, thereby potentially exposing your personal information and compromising your anonymity.
Secondly, the more nodes you connect to within the Tor network, the slower your webpage loading speeds become, rendering your browsing experience considerably slower than the norm. This consequence arises due to the transmission methodology employed by the Tor network. The encryption and forwarding of data through multiple nodes inherently impart a certain degree of impact on browsing speed.
Of paramount importance is the recognition that Tor does not guarantee absolute anonymity. The primary quandary lies with Tor exit nodes. These nodes facilitate the monitoring of any unencrypted communication protocols, such as SMTP, FTP, and HTTP, thereby encompassing sensitive information like cookies, login credentials, passwords, uploaded and downloaded files, and more. Consequently, even when utilizing Tor, cautious handling of personal information remains imperative to avert the inadvertent leakage of sensitive data.
VPN

A Virtual Private Network (VPN) is a service designed to safeguard your personal data during internet usage. The service establishes a connection to the web via your regular internet connection, with the key distinction lying in encryption. All data transmitted through a VPN undergoes encryption, offering a straightforward means of preserving anonymity and concealing your identity. However, it is important to recognize that a VPN does not provide absolute security.
For individuals engaged in computer-based work who seek access to blocked websites, there are options to install a dedicated program (VPN client) on their computer or employ a browser extension. Nevertheless, this approach entails several noteworthy drawbacks:
Firstly, a VPN can potentially impede internet speeds. Due to the time required for encryption and the often extended distances that traffic must traverse, this may be attributed to the remote location of the VPN server.
Secondly, intermittent traffic bursts may occur on the public network when utilizing a VPN connection. Failing to promptly notice these connection drops and data leaks can prove inconvenient, as the VPN connection may not automatically resume.
Furthermore, DNS queries typically rely on public network DNS servers, as opposed to virtual, secure counterparts. If these servers provide incorrect responses, users may be directed to fraudulent addresses for requested domains. Thus, vigilance is essential to avert redirection to deceptive online banking platforms and other fraudulent sites. Additionally, the use of DNS servers can potentially reveal the user's approximate geographical location and internet service provider.
Lastly, various legal considerations come into play. Legislation varies across jurisdictions, and VPN clients and servers are often situated in different countries, with traffic potentially transiting through third-party nations. Consequently, it is possible for copies of transmitted data to be retained for subsequent decryption. Hence, the utilization of VPN services necessitates caution and compliance with local laws and regulations.
Use the Proxy

A proxy server, often referred to as an intermediary, fulfills the precise role of mediating between the user and the ultimate server. In this capacity, the intermediary may not necessarily possess knowledge of the parties involved. Proxy servers facilitate the indirect transmission of requests to other servers and the reception of responses from them.
Employing a web proxy enables anonymous web browsing, as data traverses multiple servers situated across diverse regions worldwide. This intricate routing makes it arduous for attackers to track your IP address, a crucial element in preserving personal privacy.
A secure proxy server functions as a conduit between your computer and the websites you visit. By connecting through a proxy, you gain notable advantages, including anonymity, privacy, and a sense of unrestricted liberty.
Nonetheless, it is crucial to acknowledge that connecting through a proxy server solely allows for the concealment of your IP address. They do not encrypt internet traffic during transit, thereby enabling internet service providers (ISPs) to still observe your online activities. Consequently, exercising vigilance is essential when utilizing a proxy server.
Proxy servers prove beneficial in situations where concealing your location is imperative, such as accessing online stores that offer substantial discounts restricted to specific countries. However, it is essential to note that websites can employ over 100 parameters to track and potentially disclose your identity. For heightened anonymity and data protection, it is advisable to combine the use of a Lalicat anti-detection browser with a proxy server, thereby augmenting online privacy and security.
Lalicat browser
- the optimal solution
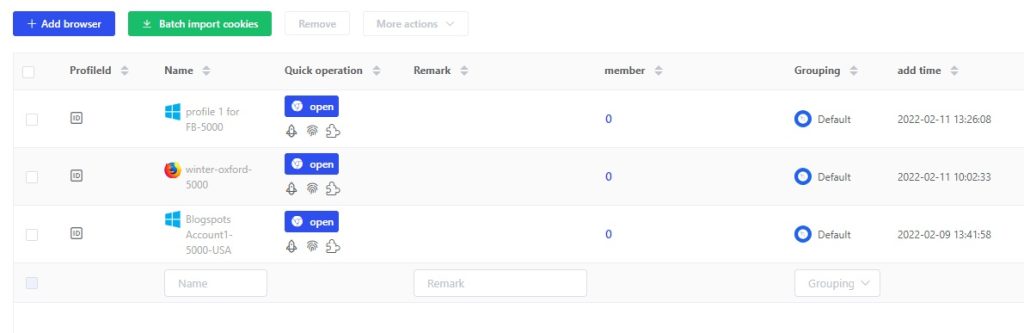
The Antidetect Browser presents a distinctive approach to internet browsing by offering an alternative browser fingerprinting program. This program enables users to operate multiple advertising or social accounts concurrently. With the aid of anti-detection browsers like Lalicat, you gain the ability to modify all connection parameters, specifying which parameters the website should perceive while concealing those you desire to keep private.
These parameters encompass a broad range of factors, including screen resolution, time zone, color depth, CPU class, platform, installed fonts, plugins, Adblock settings, pixel ratio, and utilization of Canvas Blocker, among others. Through the manipulation of these parameters, the antidetect browser proficiently obscures your authentic identity and location, thereby safeguarding your online privacy and enhancing your overall security.
Leveraging an anti-detection browser yields numerous advantages, such as preventing tracking, mitigating the risk of being hacked, preserving personal privacy, safeguarding corporate secrets, and more. Moreover, it enables the seamless operation of multiple accounts concurrently, alleviating concerns regarding account bans or restrictions.
Why is it superior to others?

Devotees of the Antidetect browser are enamored by the convenience and user-friendly nature of Lalicat, as it is built upon the Chromium framework, rendering it just as convenient and straightforward to navigate as a conventional browser. Its performance remains swift and unhindered, akin to browsing without any anonymity tools. For individuals necessitating the simultaneous utilization of multiple accounts, it is advisable to procure a proxy from a reputable provider. By employing high-quality proxies, you can ensure absolute anonymity.
Lalicat further offers a complimentary trial period, instilling confidence in the efficacy of this tool and allowing users to select the subscription plan that best aligns with their requirements. It presents a three-day free plan that grants unrestricted access to all its features. Users of Lalicat benefit from comprehensive anonymity protection, thereby fortifying their personal privacy and enhancing their overall security.
The amalgamation of an anti-detection browser and a proxy server serves to bolster online privacy and security significantly. Not only does it enable the concealment of real identities and locations, but it also serves as a deterrent against tracking, fends off malicious hackers, safeguards corporate trade secrets, and delivers a host of additional advantages.
Additional measures
- Temp email

When sending an email, it is highly probable that your identity becomes susceptible to exposure. This vulnerability arises from the fact that your genuine IP address is stored on the mail server. Consequently, entities like Google and other companies may disclose your actual IP address upon receiving a request from governmental or authoritative bodies. Moreover, data breaches occur intermittently, potentially allowing unauthorized individuals to uncover your physical location and, in some instances, your true identity.
To fortify your online privacy and security, we strongly advocate for the utilization of temporary mail services. Temporary email entails employing an email address for a limited duration, typically for the purpose of receiving registration confirmations before promptly abandoning the platform, thereby resulting in the automatic deletion of the temporary email. However, it is also possible to find temporary mail services that offer validity spanning a few days.
Adopting a temporary email approach empowers you to safeguard your privacy and evade tracking or hacking endeavors. Furthermore, it enables you to circumvent the influx of spam emails and promotional advertisements, enhancing the overall efficiency of email usage.
- Anonymous Payment

A myriad of options exists when it comes to selecting an anonymous payment system. For those seeking comprehensive management of their electronic accounts while maintaining absolute anonymity, the utilization of cryptocurrencies emerges as the optimal choice. Cryptocurrencies operate without centralized data centers, ensuring that financial transactions remain impervious to track, thereby safeguarding personal privacy and bolstering overall security. Among the various cryptocurrencies, Bitcoin stands as the most renowned, and establishing your own crypto wallet is as straightforward as acquiring a debit card.
Upon wallet creation, the acquisition of cryptocurrencies can be facilitated through prominent exchanges. The prevalence of these exchanges often serves as a testament to the trust vested by users within the system. Once in possession of the desired cryptocurrency, prompt transfers and payments for services can be executed. The option to conduct transactions using cryptocurrencies has gained significant traction, with a growing number of companies now embracing Bitcoin as a viable form of payment.
get free trial
We Offer 3-Day Free Trial for All New Users
No Limitations in Features