Rò rỉ trình duyệt: Bảo vệ quyền riêng tư trực tuyến và ngăn chặn khai thác
A private data leak represents an extremely grave violation of information security, posing a significant peril to your personally identifiable information (PII). This sensitive data encompasses crucial particulars like your birth date, social security number, email address, username, password, residential address, phone number, and medical records, among others. If this valuable information were to fall into the wrong hands, it could be exploited for nefarious purposes such as various types of identity theft, cyber assaults, and impersonation on social media platforms.
These private data leaks not only cause substantial harm to the individuals affected but also constitute a menace to the online privacy of the general populace. Once such information becomes exposed on the Internet, it can be disseminated without restriction and may even surface on the dark web. This data is persistently repurposed, thereby exacerbating our vulnerability to online security hazards.
Frequent reasons for
data leaks
The predominant cause of data leaks stems from inadequate data security practices, and this inescapable reality demands our attention. From feeble passwords to unprotected databases and misplaced devices, the cumulative effect of these security leaks poses an immense threat. Given the intricate and interconnected nature of modern technology, errors, be they human or technical in nature, are bound to occur. Despite the extensive efforts of experts working diligently behind the scenes to avert such incidents, completely eradicating the risk is an arduous task.
Cognizant of this fact, malicious hackers actively exploit both longstanding and emerging vulnerabilities to infiltrate systems, exploiting weaknesses inherent to human behavior, software, hardware, and business protocols. An attack of this nature not only exposes personally identifiable information (PII), but also affords assailants a comprehensive understanding of a target's defensive vulnerabilities, enabling them to strategize for subsequent assaults.
As technology advances and data continues to proliferate, the risk of data leaks escalates. Cybercriminals remain perpetually vigilant for inadvertent data leaks as they serve as opportunities to expand their reservoir of potential victims and formulate strategies for future attacks. This alluring prospect, requiring minimal effort yet yielding high-potential returns, cannot be disregarded.
In the face of diverse forms of breaches, it is imperative that we exercise heightened vigilance to ward off scams that aim to target us, safeguarding our personal information and assets from compromise. Here are several prevalent types of scams that warrant particular attention:
First and foremost is phishing email, an insidious scheme designed to deceive individuals into clicking on malicious links, opening attachments, or divulging sensitive personal information, such as passwords for banking cards. Exploiting emotions like fear, excitement, or trust in reputable entities, attackers employ convincing pretexts to solicit financial details or manipulate victims into visiting malevolent websites.
The second is voice phishing, an artifice wherein attackers employ telephone calls to dupe individuals into transferring money, revealing confidential information, or otherwise furnishing advantages to the perpetrators. By assuming the guise of banks, government agencies, or other trustworthy entities, these malefactors exploit trust to achieve their objectives.
Possible results of data leaks
Cyber adversaries perpetually seek opportunities to establish counterfeit social media accounts under our identities, employing them as tools to defraud our family, friends, colleagues, and acquaintances. This insidious act of social media impersonation can inflict severe harm upon our reputation, relationships, as well as our professional and business endeavors.
However, one of the most pernicious consequences of private data breaches manifests in the form of digital identity theft. Cybercriminals acquire comprehensive insights into our online footprints, thereby gaining access to valuable information pertaining to our lives and assets. The more these malefactors learn, the easier it becomes for them to pilfer our identities and exploit them for obtaining credit cards, applying for loans, and even perpetrating illicit activities under our names.
Adding to the frustration, once private data becomes leaked into the online realm, our personal details become amalgamated with other publicly accessible information derived from sources like social media platforms, search engines, or public databases. This amalgamation occurs within servers under the control of cybercriminals, where the data is traded on darknet forums and persists in backups and diverse repositories, rendering its retrieval or erasure an irrevocable endeavor.
What are browser leaks?
The exchange of information plays an indispensable role in the everyday functioning of the contemporary internet. Nevertheless, it is imperative to recognize that certain data is of a private nature and necessitates safeguarding by the browser. Regrettably, browsers occasionally inadvertently disclose this crucial information, resulting in compromised privacy and frequently entailing web fingerprinting.
Browser leaks demand our earnest attention as they have the potential to expose personal information and location, thereby rendering them exploitable by malicious actors. The following are notable categories of browser leaks:
Firstly, there are IP address leaks, whereby your browser may divulge your IP address, enabling third parties to glean details such as your current status, internet service provider (ISP), region, and even city. This is an issue that warrants significant concern.
Secondly, we have WebRTC leaks. In certain instances, the WebRTC API can be exploited to unveil your real IP address, even if you are utilizing a virtual private network (VPN). Consequently, exercising utmost caution during any online WebRTC leak testing is paramount.
JavaScript also represents a contributing factor to browser leaks. While this technique is commonly employed on dynamic web pages, it can inadvertently disclose certain information, including your system resolution, current time, and web browser.
Lastly, geolocation presents another area of concern. Modern browsers generally support geolocation functionality, which may reveal your present whereabouts. Browsers often request permission to access your current location, and it is advisable to deny such requests in order to maintain your security.
How to prevent browser leaks?
- Avoid using browser extensions
In the realm of the internet, we have facile access to diverse browser extensions that augment our browsers with supplementary functionalities, such as comment authenticity detection or grammar correction. Nevertheless, these extensions can harbor vulnerabilities that malevolent hackers may exploit to gain unauthorized access to our personal information. In the event that extension developers neglect to maintain timely updates, users of such extensions become potential targets for hackers.
To safeguard our personal information and privacy, it is incumbent upon us to consistently assess the extensions we have downloaded and deactivate those that are seldom or never utilized. By navigating to our browser settings, we can meticulously review the extensions in our possession and disable or delete them as necessary.
Simultaneously, we can actively seek out reputable publishers and opt for extensions that adhere to Google's technical best practices concerning user experience and design. In an effort to enhance the discoverability of these trusted extensions, Google has introduced badges on extension listings within the Chrome Store, signifying their provenance from reputable publishers. A check mark badge accompanying a developer's name denotes a well-established publisher with an untarnished record devoid of violations. A featured badge indicates that the extension aligns with Google's technical best practices for user experience and design. These badges serve as invaluable aids in identifying trustworthy extensions while mitigating the risk of unwittingly downloading potentially malicious ones.
Lastly, it is imperative to periodically update both our browsers and extensions to ensure that we are utilizing the latest iterations and that any known vulnerabilities have been rectified in a timely manner. Only through these proactive measures can we effectively fortify the security of our personal information and privacy, effectively thwarting hacker incursions.
- Change browser fingerprints
During our online browsing, websites frequently make inquiries to our browsers, seeking information such as location, hardware specifications, screen size, installed fonts, and browser version. The purpose of these queries is to ensure the accurate loading of web pages. However, when combined, this amalgam of data forms a distinct "fingerprint" that is unique to our specific browser, enabling highly effective tracking of our online activities, even in cases where traditional trackers have been disabled. By utilizing fingerprinting tools, we can evaluate the level of uniqueness inherent in our browser fingerprints and take proactive measures to safeguard our online privacy.
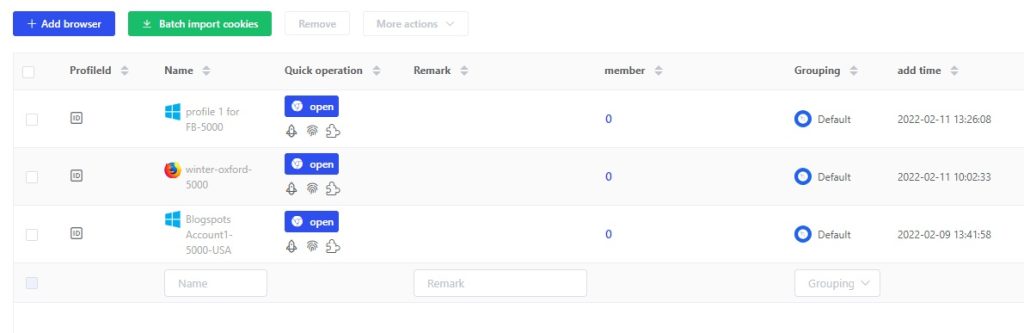
In theory, preventing fingerprinting entails utilizing a device that shares similar settings and configurations with the majority of users. For instance, iPhones offer a higher degree of privacy compared to Android devices due to their relatively lesser customization and uniqueness, whereas Linux users exhibit greater individuality in contrast to Chrome users. As an alternative approach, we have the option to employ anti-detection browser tools that generate browser fingerprints in a random manner. By obfuscating browser characteristics, we can effectively mitigate the risk of identification and tracking by advertisers, data analysts, and other trackers. This comprehensive approach enhances the security of our online privacy, granting us a more liberated and anonymous web browsing experience.
- Be cautious about browser autofill
The autofill functionality of web browsers is intended to streamline the process of completing form fields that require laborious information, such as names, addresses, and dates of birth. This convenience often outweighs concerns about browser security when it comes to saving this information.
However, in the past, browsers have been manipulated to disclose stored personal data without the user's knowledge. Malicious websites employ hidden text boxes with encoded scripts and seemingly innocuous requests, such as offering a discount, as a ruse to perpetrate phishing attacks. As users input information, the autofill feature appends additional data stored in the browser's autofill repository, which may contain sufficient details to facilitate illicit activities like credit card fraud.
This exploitation of autofill functionality is undoubtedly troubling, yet it does not necessitate complete abandonment of its usage. Instead, it is advisable to undertake certain essential measures to safeguard our personal information:
Regularly review browser autofill settings: Ensure that only essential information is stored, deleting any outdated data that is no longer necessary.
Keep your browser up to date: Maintain the latest version of your browser to avail yourself of the most recent security patches and feature enhancements.
Exercise caution with autofill prompts: Thoroughly scrutinize the information displayed in autofill prompts to ensure that only accurate and relevant details are filled into the corresponding form fields.
Remain vigilant against phishing attacks: Exercise utmost vigilance and exercise caution while interacting with links and pop-ups from untrustworthy sources, avoiding falling prey to phishing traps.
Consider using a password manager: Evaluate the adoption of a reliable password manager that securely stores and autofills your login credentials, reducing reliance on browser autofill functionality.
- Prioritize HTTPS websites
When you visit a website without the "https" prefix, it means that all your actions on that site, such as clicking and typing, are susceptible to eavesdropping. While this may not be an issue for sites that solely display public content, it poses a significant problem for websites that involve the input of personal information like login credentials, social security numbers, or other sensitive data. In such cases, anyone can potentially spy on your information.
To compound the issue, certain websites may employ the "https" prefix on their home pages but revert to the insecure "http" protocol on other pages. This poses a grave risk, particularly on pages that require passwords or payment details.
To safeguard your personal information and uphold your privacy, it is crucial to verify that websites employ the "https" prefix and ensure the presence of a secure padlock icon before entering any sensitive data. Modern browsers such as Chrome, Edge, Safari, and Firefox recognize sites with a padlock as secure, while insecure sites are flagged as unsafe (often depicted with a red padlock) and accompanied by an alert displayed adjacent to the URL bar.
For enhanced online privacy and security, it is advisable to consider downloading the HTTPS Everywhere extension for browsers like Firefox, Chrome, and Edge. This extension automatically encrypts communications between your browser and major websites, shielding your personal information from eavesdroppers and prying eyes. Although the extension cannot compel all connections to utilize "https," it automatically converts any detected insecure "http" links to secure "https" links, offering an added layer of protection.
FAQs
What are browser leaks?
Browser leaks occur when browsers unintentionally reveal private information, potentially compromising privacy and enabling web fingerprinting. This can involve disclosing IP addresses, WebRTC information, system details, and geolocation data.
How do IP address leaks happen?
IP address leaks occur when a browser exposes the user's IP address to third parties. This information can reveal details such as the user's location, internet service provider (ISP), and even city.
What are WebRTC leaks?
WebRTC leaks involve the Web Real-Time Communication (WebRTC) API, which can inadvertently reveal the user's real IP address, even when they are using a virtual private network (VPN). This can potentially bypass the anonymity provided by the VPN.
What are geolocation leaks?
Geolocation leaks occur when browsers support geolocation functionality and request permission to access the user's current location. Granting such permission can expose the user's whereabouts, potentially compromising their privacy.
dùng thử miễn phí
Chúng tôi cung cấp 3 ngày dùng thử miễn phí cho tất cả người dùng mới
Không có giới hạn về tính năng